Secure read-only access to crypto wallets
Share access to your portfolios without ever exposing keys or execution permissions. Offer your clients complete transparency while maintaining full control.
The problem
Giving access to a crypto portfolio often involves a trade-off between transparency and security. Sharing full access exposes you to operational risks, while no access limits client trust.
CIYL's response
Read-only mode allows secure access to portfolios without authorizing any actions. Users can view data in real-time without ever being able to execute operations.
What is read-only mode for?
This feature allows sharing information without exposing infrastructure. It creates a balance between client visibility and operational security.
- Give access to a portfolio without execution authorization
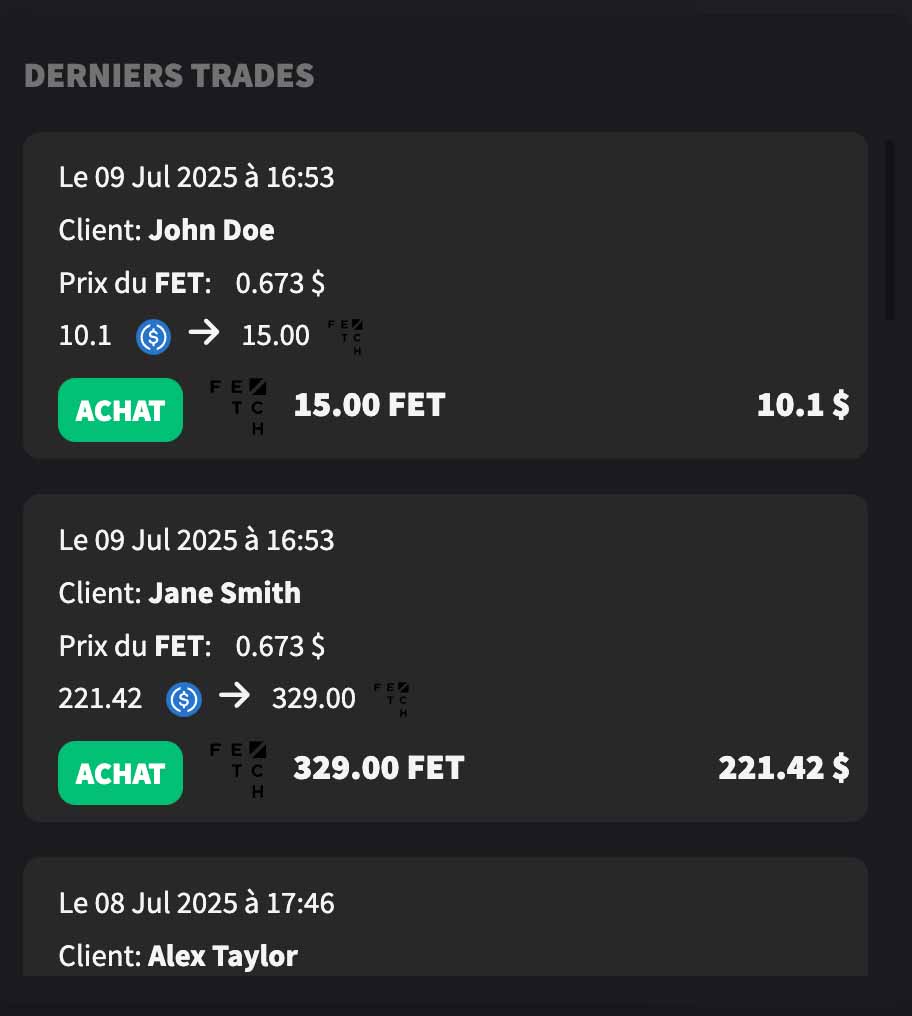
- Share real-time performance with a client
- Maintain total control over assets
- Avoid any external manipulation or error
- Strengthen transparency without compromising security
Why this feature is essential
Maximum security
No orders can be executed. Access is strictly limited to consultation.
Client transparency
Clients can track their assets in real-time without depending on external reports.
Total control
The manager maintains complete mastery of operations and infrastructure.
Risk reduction
Eliminates human errors from poorly configured or shared access.

A standard for professionals
Professional managers never share access with execution capability. Read-only mode meets this requirement while offering complete transparency.
- No interaction possible with funds
- Controlled and secure access
- Real-time visibility for clients
- Adapted to multi-client environments
Typical use cases

Family office
Client transparency without asset exposure - Give your clients complete visibility into their portfolios while maintaining full control over operations.

Manager
Secure sharing with investors - Allow investors to track their positions without ever exposing execution access or sensitive keys.

Reporting
Direct access to real-time data - Eliminate manual reports and offer permanent access to performance and exposure data.
Complementary features
Centralize portfolio tracking and combine it with other secure sharing modules.
FAQ
Does read-only mode allow executing transactions?
No. It is strictly limited to consultation. No actions can be taken.
Is it secure to share read-only access?
Yes. Permissions are limited to viewing, eliminating risks associated with operations.
Can this access be shared with multiple users?
Yes. Multiple accesses can be configured according to tracking or reporting needs.
Why use this mode rather than classic reporting?
It offers real-time transparency, without depending on periodic reports or external consolidations.
Secure the sharing of your crypto portfolios
- Share access without exposing your assets
- Offer real-time transparency to your clients
- Fully control access and permissions
- Reduce risks associated with sharing information